Facial Recognition vs Alternatives for Solar Security
SOLAR TODO
Solar Energy & Infrastructure Expert Team
Watch the video
TL;DR
For critical infrastructure, do not start with facial recognition as the default. Use it only at controlled access points where lighting and subject position are predictable. Most off-grid sites get better protection from layered systems using 16 cameras, 32 detector points, perimeter sensing, and 24-48 hours of battery autonomy. SOLAR TODO typically recommends matching analytics to each zone’s task, then selecting FOB, CIF, or EPC delivery based on project scope.
Solar-powered security systems for critical infrastructure work best when facial recognition is matched to site risk, not used by default: 32-zone off-grid designs support 16 cameras and 24/7 monitoring, while EPC delivery typically ranges from USD 7,100-9,200 for medium remote sites.
Summary
Solar-powered security systems for critical infrastructure work best when facial recognition is matched to site risk, not used by default: 32-zone off-grid designs support 16 cameras and 24/7 monitoring, while EPC delivery typically ranges from USD 7,100-9,200 for medium remote sites.
Key Takeaways
- Match facial recognition to controlled entry points with at least 1 cooperative capture zone, because accuracy drops when subjects are moving fast, backlit, or wearing PPE.
- Use layered detection with 16 cameras, 32 detectors, and 32 active alarm zones when protecting border posts, substations, pipelines, or telecom compounds.
- Size off-grid power for 24/7 operation with battery autonomy of at least 24-48 hours, especially where grid uptime is below 95%.
- Compare analytics options by task: use facial recognition for identity verification, LPR for vehicle lanes, and perimeter beams or dual-tech detectors for 50-200 m boundary segments.
- Reduce nuisance alarms by combining 8 perimeter beam sets, 16 PIR units, and 16 dual-technology detectors instead of relying on video motion alone.
- Budget using 3 tiers: FOB supply, CIF delivered, and EPC turnkey, with volume discounts of 5% at 50+ units, 10% at 100+, and 15% at 250+.
- Verify compliance with EN 50131, IEC 62676, UL 681, and NFPA 72 when specifying alarm logic, video retention, installation practice, and supervisory signaling.
- Plan ROI around avoided guard hours, fewer false dispatches, and better evidence retention, with payback commonly driven by 1-3 labor positions or reduced incident loss.
Facial Recognition vs Alternatives for Critical Infrastructure
Facial recognition is most effective at 1-3 controlled access points, while perimeter protection across 32 zones usually depends more on cameras, detectors, and alarm logic than on identity analytics alone.
Critical infrastructure buyers often ask whether facial recognition should be the primary layer in a solar-powered security and surveillance system. The short answer is no for most remote or mixed-risk sites. Facial recognition solves a narrow problem: verifying identity at a gate, lobby, control room, or staff entrance where the camera angle, standoff distance, and lighting can be controlled within a repeatable range such as 1-3 m. It does not replace perimeter intrusion detection, vehicle screening, or wide-area situational awareness.
For border checkpoints, power towers, telecom compounds, substations, and remote utility assets, the selection process should start with threat pathways and site geometry. A medium remote site may need 16 cameras, 32 detector points, and a 64-zone hybrid panel with 32 active zones plus 32 spare zones for expansion. In that layout, facial recognition may cover only 2-4 doors or 1 main gate, while the rest of the site depends on fixed cameras, PTZ cameras, beam sets, PIR sensors, dual-technology detectors, and event-driven recording.
According to the International Energy Agency, “Solar PV is today one of the cheapest sources of electricity in many regions,” which matters when remote security systems must run 24/7 without stable grid supply. According to NREL (2024), solar resource modeling can predict site energy yield with bankable methodology, which helps buyers size battery autonomy and camera uptime before procurement. For critical infrastructure, the question is not whether facial recognition is advanced enough; the real question is whether it is the best use of power, bandwidth, and project budget at each layer of the site.
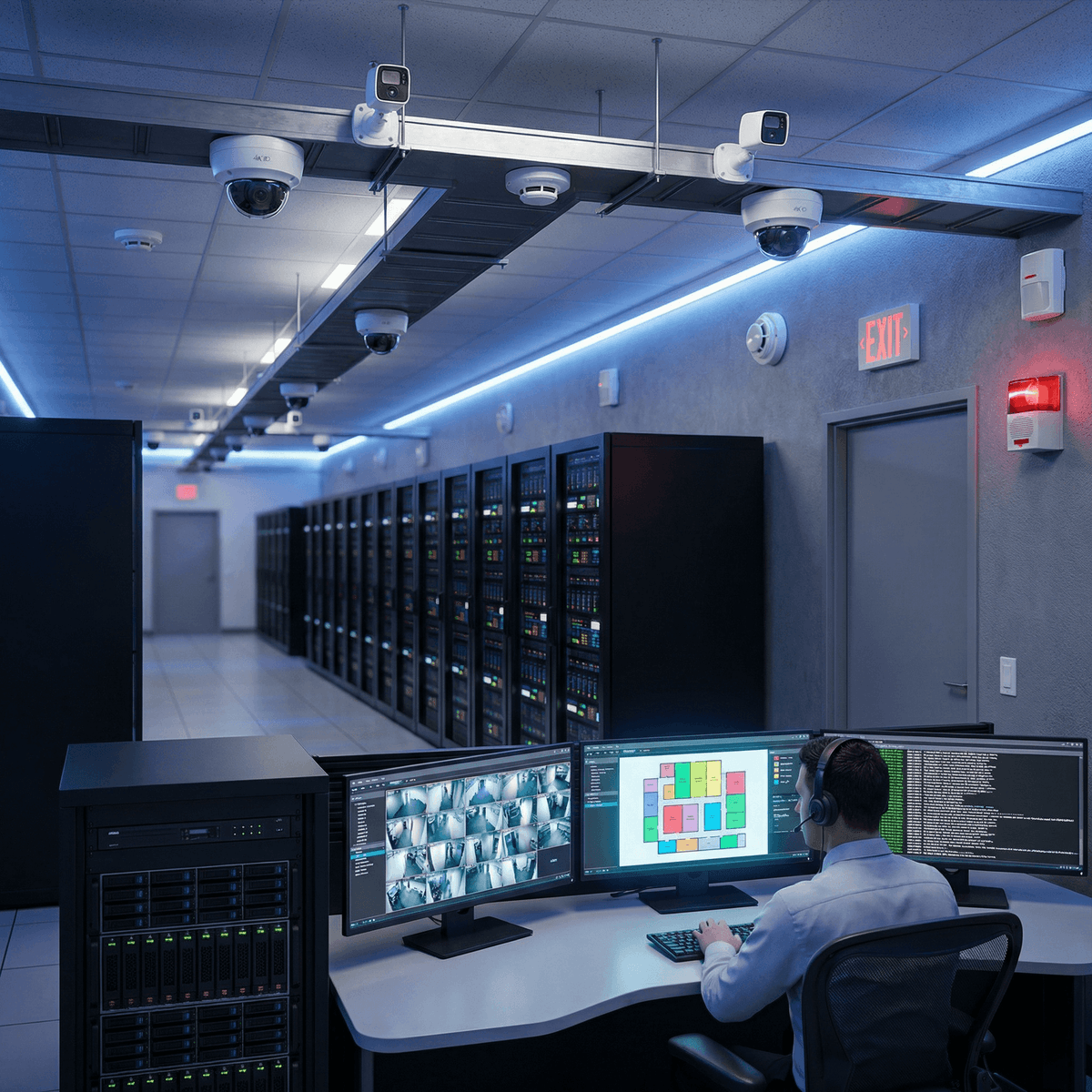
System Architecture for Solar-Powered Security Sites
A practical off-grid architecture combines 12 fixed IP cameras, 4 PTZ cameras, 32 detector points, and a 32-channel NVR so surveillance, alarm verification, and incident recording continue through 24-hour operating cycles.
A solar-powered security system for critical infrastructure has 4 linked layers: power generation, energy storage, detection, and command logic. On the power side, the design usually includes a PV array, MPPT charge control, battery storage, DC distribution, surge protection, and inverter capacity where AC loads are unavoidable. On the security side, the design includes cameras, NVR, alarm panel, communication links, and field devices such as beam sets, PIRs, door contacts, or dual-tech detectors. If any one layer is undersized by 10-20%, the whole site can lose uptime.
For a checkpoint or remote utility compound, SOLAR TODO commonly positions facial recognition as an access-control function rather than a full-site detection strategy. A sample medium-security layout may include 12 HD fixed IP cameras for lane views, building entrances, and perimeter corners; 4 PTZ cameras for operator-controlled zoom; 8 perimeter beam sets for linear boundaries; 16 PIR detectors for indoor or sheltered spaces; and 16 dual-technology detectors for thermally unstable or wind-prone zones. This structure gives both broad coverage and event confirmation.
Where facial recognition fits
Facial recognition works best where the subject cooperates or can be slowed down. Examples include staff turnstiles, badge-assisted doors, inspection offices, and secure records rooms. In these conditions, the camera can hold a stable angle, the face can fill enough pixels for matching, and supplemental white light or IR can keep image quality consistent over 24 hours. If workers wear helmets, masks, goggles, or scarves, match rates can fall and manual verification should remain available.
Where alternatives perform better
Alternatives often outperform facial recognition in remote critical infrastructure because they answer different operational questions. LPR identifies vehicles in 2-4 lanes. PTZ cameras support operator tracking over 100 m or more. Perimeter beams secure fence lines and sterile zones. Dual-tech detectors reduce false alarms where heat shimmer, rain, or vegetation movement affect PIR-only devices. A 64-zone hybrid panel also allows spare capacity for future fence vibration sensors, panic buttons, or relay outputs from thermal analytics.
According to IEC 62676, video surveillance design should consider image quality, scene purpose, and operational use rather than camera count alone. According to UL 681, installation practice and system classification matter because poor field layout can undermine otherwise capable devices. That is why SOLAR TODO usually recommends layered architecture first, then analytics selection second.
Comparing Facial Recognition with Alternative Detection Methods
For most critical infrastructure sites, facial recognition covers 5-15% of the protected area but can consume a disproportionate share of integration effort if used outside controlled capture conditions.
The right comparison is not facial recognition versus one single competitor. Buyers should compare it against a stack of alternatives that each serve a different detection or verification task. A substation gate, for example, may need identity verification for staff, but the perimeter still needs intrusion detection across 100-500 m, and the vehicle lane still needs plate capture or under-vehicle inspection. One analytics tool cannot do all 3 jobs with equal reliability.
| Method | Best use case | Typical coverage | Power/bandwidth demand | Main limitation | Best fit in solar-powered sites |
|---|---|---|---|---|---|
| Facial recognition | Staff or visitor identity at doors/gates | 1-3 controlled points | Medium to high | Sensitive to angle, lighting, PPE, occlusion | Access control at inspection rooms, admin entries, control rooms |
| LPR/ANPR | Vehicle lanes and fleet logging | 2-4 lanes per site | Medium | Less useful for pedestrians | Border lanes, fuel depots, utility yards |
| Fixed HD IP cameras | General surveillance and evidence | Wide static scenes | Medium | Limited detail at long distance | Perimeter corners, doors, cashier zones, lane overview |
| PTZ cameras | Long-range tracking and operator response | 100 m+ visual tracking | Medium to high | Requires active monitoring or presets | Border strips, substations, large compounds |
| Perimeter beam sets | Fence line intrusion detection | 50-200 m segments | Low | Requires alignment and clear path | Remote compounds, sterile zones |
| PIR detectors | Indoor or sheltered motion detection | Room or corridor level | Low | More nuisance alarms outdoors | Buildings, container rooms, offices |
| Dual-tech detectors | Unstable environmental zones | Room, bay, or semi-open area | Low to medium | Higher unit cost than PIR | Wind-prone doors, loading bays, utility rooms |
From a procurement view, the comparison should include not only detection quality but also power budget, storage retention, and communication resilience. Facial recognition often needs higher image quality, better front lighting, and tighter angle control than standard surveillance. In an off-grid site, every extra watt affects battery sizing. If a site needs 24-48 hours of autonomy, adding high-compute analytics at multiple edge points can raise battery and PV requirements by a meaningful margin.
The National Institute of Standards and Technology states that face recognition performance varies significantly with image quality, demographics, and operational scenario, which is why controlled capture matters. The International Electrotechnical Commission states, through IEC 62676 guidance, that surveillance systems should be specified by operational task such as monitoring, detection, recognition, or identification. Those two points support a practical rule: use facial recognition only where identification is truly required and where the scene can be controlled.
Use Cases and Selection Guidance by Infrastructure Type
Border posts, government compounds, gas stations, and telecom or power assets need different mixes of identity control, perimeter sensing, and 30-day video retention to meet operational and evidentiary requirements.
At border checkpoints, the main risk is mixed: pedestrian access, vehicle lanes, perimeter crossing, and staff movement all happen in the same site. Here, facial recognition is useful at the inspection building, staff door, or primary gate office, but lane control usually benefits more from LPR and overview cameras. A 32-zone off-grid package with 16 cameras, 32 detectors, and a 32-channel NVR is often a better fit than a facial-recognition-heavy design because it covers more threat pathways with less dependence on ideal capture conditions.
For government buildings, the balance shifts toward identity assurance and internal zoning. A 128-zone architecture with 64 cameras and 128 detector points can segment lobbies, records rooms, executive offices, evidence storage, and IT rooms. In that case, facial recognition may add value at 4-12 controlled entrances, while fixed cameras, PTZ units, and alarm partitions handle the rest of the building. According to manufacturer and integrator benchmarks cited in the intelligent surveillance market, layered AI video analytics can reduce nuisance alarms by up to 90% versus motion-only legacy CCTV in some deployments.
For gas station portfolios, facial recognition is usually secondary to multi-site visibility, cashier protection, and forecourt oversight. A cloud-connected 32-zone package with 16 HD IP cameras, 30 days of 4K video retention, and 4G plus Ethernet plus WiFi communications gives central teams a stronger operational benefit than face matching at every site. Hazardous fuel areas also require careful device placement, cable routing, and alarm logic around 6-12 critical risk points per station.
For telecom towers, power towers, and remote energy assets, the strongest case for facial recognition is often weak unless there is a staffed shelter or controlled maintenance room. These sites usually gain more from perimeter beams, fixed cameras, PTZ verification, and low-power alarm devices because power autonomy and communication efficiency are critical. SOLAR TODO generally advises buyers to reserve facial recognition for assets with frequent authorized personnel movement and a clear need for identity logging.
EPC Investment Analysis and Pricing Structure
A three-tier model of FOB supply, CIF delivered, and EPC turnkey lets buyers align capital cost, logistics scope, and site risk, with medium off-grid checkpoint projects commonly budgeted at USD 7,100-9,200 for turnkey delivery.
For B2B procurement, EPC means Engineering, Procurement, and Construction. In practice, this includes system design, equipment selection, bill of materials, logistics coordination, installation, commissioning, and acceptance testing. Depending on country and project scope, EPC may also include cable schedules, pole or mast layouts, battery sizing, NVR and alarm configuration, and operator training. For critical infrastructure, the value of EPC is risk reduction: fewer interface gaps between power, surveillance, and alarm trades.
The standard commercial structure is usually split into 3 tiers:
- FOB Supply: equipment only, ex-works or port-based handover for buyers with local installers.
- CIF Delivered: equipment plus freight and insurance to destination port for buyers managing local construction.
- EPC Turnkey: full delivery including installation, commissioning, and acceptance support.
For the Border Checkpoint 32-Zone Off-Grid package, SOLAR TODO can supply equipment-only, delivered cargo, or turnkey EPC at USD 7,100-9,200 depending on final scope, communication options, and local installation conditions. Larger government-scale systems with 128 zones and 64 cameras fall into a different budget class, with turnkey ranges such as USD 36,300-46,600 where installation complexity, zoning, and retention requirements are much higher.
Volume pricing guidance for repeat procurement is typically:
- 50+ units: 5% discount
- 100+ units: 10% discount
- 250+ units: 15% discount
Payment terms are commonly 30% T/T and 70% against B/L, or 100% L/C at sight. Financing may be available for large projects above USD 1,000K. For quotation support, buyers can contact [email protected] or call +6585559114.
ROI should be calculated against the alternative the buyer would otherwise fund. For remote sites, that often means guard labor, diesel generation, false dispatches, or incident loss. Sample deployment scenario (illustrative): if a site avoids 1 guard position costing USD 600-1,200 per month and reduces diesel runtime by 4-8 hours per day, payback can fall into a 12-36 month range depending on battery size, communication fees, and local labor rates. The strongest ROI usually comes from combining solar autonomy with layered detection, not from facial recognition alone.
Selection Checklist for Procurement Teams
The best selection method is to score each site on 6 criteria—identity control, perimeter length, vehicle traffic, power stability, communications, and evidence retention—before choosing facial recognition or alternatives.
Procurement teams should start with a weighted matrix rather than a vendor feature list. A practical matrix assigns 15-25% weight to power autonomy, 15-20% to perimeter coverage, 10-20% to identity control, 10-15% to communications, 10-15% to maintenance access, and 10-20% to compliance and evidence retention. This keeps the decision tied to operational need instead of software features.
A useful shortlist process is:
- Define whether the site needs identification, recognition, detection, or monitoring at each zone.
- Map 1-4 controlled entry points separately from 100-500 m perimeter segments.
- Calculate 24-48 hour battery autonomy for cameras, NVR, communications, and alarm panel loads.
- Confirm standards alignment with EN 50131, IEC 62676, UL 681, and NFPA 72 where signaling interfaces apply.
- Check whether operators can maintain lens cleanliness, beam alignment, and battery health every 3-6 months.
- Reserve facial recognition for doors, turnstiles, or inspection rooms where image capture can be controlled.
SOLAR TODO supports this approach because it lowers overspecification risk. A buyer who installs facial recognition at every edge point may spend more on compute, storage, and lighting while still missing the basic need for perimeter intrusion detection. A buyer who first secures the perimeter, then adds identity analytics only where justified, usually gets better uptime and lower total cost of ownership over 3-5 years.
FAQ
Q: What is the main difference between facial recognition and other security alternatives for critical infrastructure? A: Facial recognition verifies identity at controlled points such as doors, gates, or turnstiles, while alternatives like beam sensors, PTZ cameras, and dual-tech detectors protect wider areas. In most 32-zone remote sites, identity analytics covers only a small portion of total risk exposure. The broader system still depends on layered detection and video verification.
Q: When should I use facial recognition in a solar-powered security system? A: Use facial recognition when the site has 1-3 controlled capture points, stable lighting, and a real need to verify authorized personnel. It works best at staff entrances, inspection rooms, or control rooms where subjects can be imaged within a repeatable distance such as 1-3 m. It is less effective for open perimeters or uncontrolled outdoor movement.
Q: Why are alternatives often better than facial recognition for remote infrastructure? A: Alternatives are often better because they solve perimeter, lane, and intrusion problems with lower power demand and less dependence on image quality. Beam sets, PIRs, dual-tech detectors, and fixed cameras can protect 50-200 m segments or entire rooms continuously. For off-grid systems, that usually means better battery autonomy and lower integration cost.
Q: How many cameras and detectors does a medium off-grid checkpoint usually need? A: A common medium layout uses 16 cameras, 32 detector points, a 32-channel NVR, and a 64-zone hybrid panel configured for 32 active zones. That supports 1 primary gate area, 2-4 vehicle lanes, 1 inspection building, and 1 perimeter strip. Spare zones can be kept for future expansion such as panic buttons or fence sensors.
Q: What standards should a critical infrastructure security system comply with? A: Buyers should typically review EN 50131 for intrusion systems, IEC 62676 for video surveillance, UL 681 for installation practices, and NFPA 72 where supervisory or fire-related signaling interfaces are required. These standards do not replace local code review, but they provide a solid baseline for design, installation, and acceptance planning.
Q: How do I size solar power and batteries for 24/7 surveillance? A: Start with the total daily load of cameras, NVR, communications, and alarm devices, then add autonomy for at least 24-48 hours. Off-grid designs should also account for inverter losses, battery depth of discharge, and seasonal irradiance variation. NREL resource data or equivalent modeling should be used before finalizing the PV array and battery bank.
Q: What is the cost difference between facial recognition-heavy designs and layered alternatives? A: Facial recognition-heavy designs can increase cost through higher image-quality requirements, edge processing, lighting, storage, and integration effort. A layered 32-zone off-grid package may fit within a turnkey range of USD 7,100-9,200, while broader identity-centric designs can rise if more controlled doors, readers, or compute nodes are added. Cost should be evaluated against operational need, not software count.
Q: What does EPC turnkey include for a solar-powered security project? A: EPC turnkey usually includes engineering, procurement, installation, commissioning, and acceptance support. It may also include battery sizing, camera placement, alarm programming, communications setup, and operator training. Standard terms are often 30% T/T plus 70% against B/L, or 100% L/C at sight, with financing available for projects above USD 1,000K.
Q: How long is the payback period for solar-powered security systems? A: Payback often depends on avoided guard labor, reduced diesel use, and fewer false dispatches rather than on equipment cost alone. Sample deployment scenario (illustrative): if a remote site offsets 1 guard position and cuts generator runtime by several hours per day, payback can fall in the 12-36 month range. Actual results depend on labor cost, fuel price, and maintenance access.
Q: How much maintenance do these systems require? A: Most sites need routine checks every 3-6 months for lens cleaning, battery health, detector alignment, and communication status. Beam sets and outdoor cameras need more frequent attention in dusty or windy areas. Annual verification of alarm logic, recording retention, and backup power performance is also recommended for sites running 24/7.
Q: Can facial recognition work if staff wear helmets, masks, or goggles? A: It can work in some cases, but performance usually declines when key facial features are blocked. Sites with PPE requirements should keep alternative authentication methods such as cards, PINs, or guard verification. For industrial or border settings, this is a practical reason to treat facial recognition as one layer rather than the only access-control method.
Q: How should I choose between SOLAR TODO packages for different infrastructure types? A: Choose by risk profile and operating environment. A border checkpoint may need a 32-zone off-grid package with 16 cameras and 32 detectors, while a government complex may justify 128 zones and 64 cameras. Gas station portfolios often benefit more from cloud-connected multi-site visibility and 30-day retention than from widespread facial recognition deployment.
References
- NREL (2024): PVWatts Calculator methodology and solar resource modeling used for PV production and off-grid sizing.
- IEC 62676 (2025): Video surveillance system guidance covering operational requirements, image use, and system design principles.
- EN 50131 (2024): Intrusion and hold-up alarm system framework for zoning, signaling, and system grading.
- UL 681 (2023): Installation and classification requirements for burglary and holdup alarm systems.
- NFPA 72 (2025): National Fire Alarm and Signaling Code relevant to supervisory signaling and interface planning.
- IEA (2024): Energy market and electrification analysis supporting solar PV economics for remote infrastructure power supply.
- IRENA (2024): Renewable power generation cost analysis showing continued competitiveness of solar PV in global markets.
- NIST (2024): Face recognition evaluation findings on image quality, operational conditions, and algorithm performance.
Conclusion
For critical infrastructure, facial recognition is a targeted tool for 1-3 controlled access points, while site-wide protection usually depends on 16-camera, 32-zone layered systems with reliable solar autonomy and alarm verification.
The bottom line is simple: choose facial recognition only where identification is operationally necessary, and use alternatives for perimeter, lane, and remote asset coverage. For most off-grid projects, SOLAR TODO can deliver better total value with a layered solar-powered security and surveillance system than with a facial-recognition-first design.
About SOLARTODO
SOLARTODO is a global integrated solution provider specializing in solar power generation systems, energy-storage products, smart street-lighting and solar street-lighting, intelligent security & IoT linkage systems, power transmission towers, telecom communication towers, and smart-agriculture solutions for worldwide B2B customers.
About the Author

SOLAR TODO
Solar Energy & Infrastructure Expert Team
SOLAR TODO is a professional supplier of solar energy, energy storage, smart lighting, smart agriculture, security systems, communication towers, and power tower equipment.
Our technical team has over 15 years of experience in renewable energy and infrastructure, providing high-quality products and solutions to B2B customers worldwide.
Expertise: PV system design, energy storage optimization, smart lighting integration, smart agriculture monitoring, security system integration, communication and power tower supply.
Cite This Article
SOLAR TODO. (2026). Facial Recognition vs Alternatives for Solar Security. SOLAR TODO. Retrieved from https://solartodo.com/knowledge/facial-recognition-vs-alternatives-solar-powered-security-systems-selection-guide-for-critical-infrastructure
@article{solartodo_facial_recognition_vs_alternatives_solar_powered_security_systems_selection_guide_for_critical_infrastructure,
title = {Facial Recognition vs Alternatives for Solar Security},
author = {SOLAR TODO},
journal = {SOLAR TODO Knowledge Base},
year = {2026},
url = {https://solartodo.com/knowledge/facial-recognition-vs-alternatives-solar-powered-security-systems-selection-guide-for-critical-infrastructure},
note = {Accessed: 2026-05-13}
}Published: May 13, 2026 | Available at: https://solartodo.com/knowledge/facial-recognition-vs-alternatives-solar-powered-security-systems-selection-guide-for-critical-infrastructure
Subscribe to Our Newsletter
Get the latest solar energy news and insights delivered to your inbox.
View All Articles